| Random tidbits, thoughts, ideas, reviews, etc.Aaron Goes Yakkity Yak Photo: Close-up of Sand in BloomIPv4You are not logged in. Click here to log in. |
Here are a few of my latest Yakkity Yak web log entries. Don't forget to check out my GPS cache hunt adventures, Astounding Adventures.
Or click here for the RSS feed.
Use Google to search aarongifford.com:
Page 1 of 18
Found my Filipina Dream Woman
Thursday, 12 June 2025 8:45 PM MDT
Web Site News, Yakkity Yak
 My Dreamgirl Joan My Dreamgirl Joan Blurry AaronWhen the pandemic hit in 2020, I was still an old bachelor. Though I'd met and dated some absolutely wonderful women a decade earlier when I was attending an LDS Singles Ward (local congregation for single adults) for (at that time) ages 35-45, no long term relationships developed—though friendships did. After I "expired" from the ward's age range, still single, and returned to my local family ward (congregation), my dating life slowed nearly to a standstill. Until 2020. I was isolating at my home in Southwestern Utah, and in October, I decided to give online dating a try again and re-enabled my profile (and tweaked it with a few updates) on the Mutual LDS Dating App (think "Tinder" for Latter-day Saints). And to increase the profiles available for potential matching, I expanded my geographic range to the whole world, and increased the age range of women's profiles I was willing to consider. While exploring profiles, I saw this lovely and beautiful young Asian woman from the Philippines named Joan. Wow, she was CUTE! So of course I "swiped up"--think Tinder's swipe-right to match. But she was much younger than I was, my sister Julianne's age. When I'd dated in the Singles Ward a pretty girl much junior to me, I felt very uncomfortable about the age difference. And Joan was younger than she was. I didn't think a match would be likely. Blurry AaronWhen the pandemic hit in 2020, I was still an old bachelor. Though I'd met and dated some absolutely wonderful women a decade earlier when I was attending an LDS Singles Ward (local congregation for single adults) for (at that time) ages 35-45, no long term relationships developed—though friendships did. After I "expired" from the ward's age range, still single, and returned to my local family ward (congregation), my dating life slowed nearly to a standstill. Until 2020. I was isolating at my home in Southwestern Utah, and in October, I decided to give online dating a try again and re-enabled my profile (and tweaked it with a few updates) on the Mutual LDS Dating App (think "Tinder" for Latter-day Saints). And to increase the profiles available for potential matching, I expanded my geographic range to the whole world, and increased the age range of women's profiles I was willing to consider. While exploring profiles, I saw this lovely and beautiful young Asian woman from the Philippines named Joan. Wow, she was CUTE! So of course I "swiped up"--think Tinder's swipe-right to match. But she was much younger than I was, my sister Julianne's age. When I'd dated in the Singles Ward a pretty girl much junior to me, I felt very uncomfortable about the age difference. And Joan was younger than she was. I didn't think a match would be likely.
Then on Sunday afternoon, October 4th, after watching the final session of LDS General Conference on my television I opened up the Mutual app. There was a notification. I had a MATCH! Now I'd had matches before. Some of them were fake "Catphishing" profiles—scammers. And some were real women. The Catphishers sometimes would message me first. But none of the real girls ever did. Sadly, none of the real matches had ever quite led to dates, though a few came close. So while I was intrigued by this match, I had low expectatations. And she had send me a message first! My catphishing alarm bells were sounding. Then I clicked on the message, dated Oct. 4, 5:06 PM (Utah time was what was showing to me). It was simple: "Hi Aaron!" And it was that CUTE Filipina Asian girl, Joan! Was this real? I double-checked her profile. It looked legitimate. Catphisher profiles usually had a style that looked fake, looked catphishy. Joan's profile looked like that of a real woman with a real life. Of course I responded, though it wasn't until 7:31 PM (again my time, Utah time): "Hi Joan! Nice to meet you. how are you? I am feeling grateful, having watched general conference yesterday and today." She was ONLINE! And replied right away! We were chatting!  Joan Prepares for Wedding Joan Prepares for Wedding Aaron is Ready to WedLong story short, we soon were video dating EVERY DAY for hours at a time. And doing our LDS gospel study together, praying together. Aaron is Ready to WedLong story short, we soon were video dating EVERY DAY for hours at a time. And doing our LDS gospel study together, praying together.
Who said "I love you" first? She did, early on. And while I really, really liked her, and even was beginning to love her, I wasn't quite ready to say "I love you" in return. But just a few weeks later, I was smitten and gushed, "I love you!" easily in return. She was WONDERFUL! Oh, yeah, I was making the long story short. I got a passport. I flew to the Philippines. And we've been husband and wife for a few years now. And she is still my dream woman. I love her more and more every day! Does This Ancient Code Even Work?
Thursday, 22 July 2021 2:43 PM MDT
Yakkity Yak
It's been over eight-and-a-half years since I "'blogged" on my web site. Does my ancient and archaic web site code even work well enough that I can post something NEW? As soon as I click "Save" I will find out.
Hello, everyone! I hope you're all doing well. I'm loving life, working, playing, chatting for hours with my far-away fiancée (hoping we'll soon be together and figure out whether a fiancée K-1 visa or spouse CR-1 visa will be in our future), and wanting to get back into hiking often. Christmas 2012 Wish List for Santa
Saturday, 01 December 2012 4:59 PM MST
Yakkity Yak
Dear Santa,
Feel free to bring me any one or more of the following really awesome things for Christmas. I promise I'll be a good boy. Sincerely, Aaron Gifford P.S. Here's the list:
Knuckle Song Variation
Thursday, 09 August 2012 9:54 AM MDT
Yakkity Yak
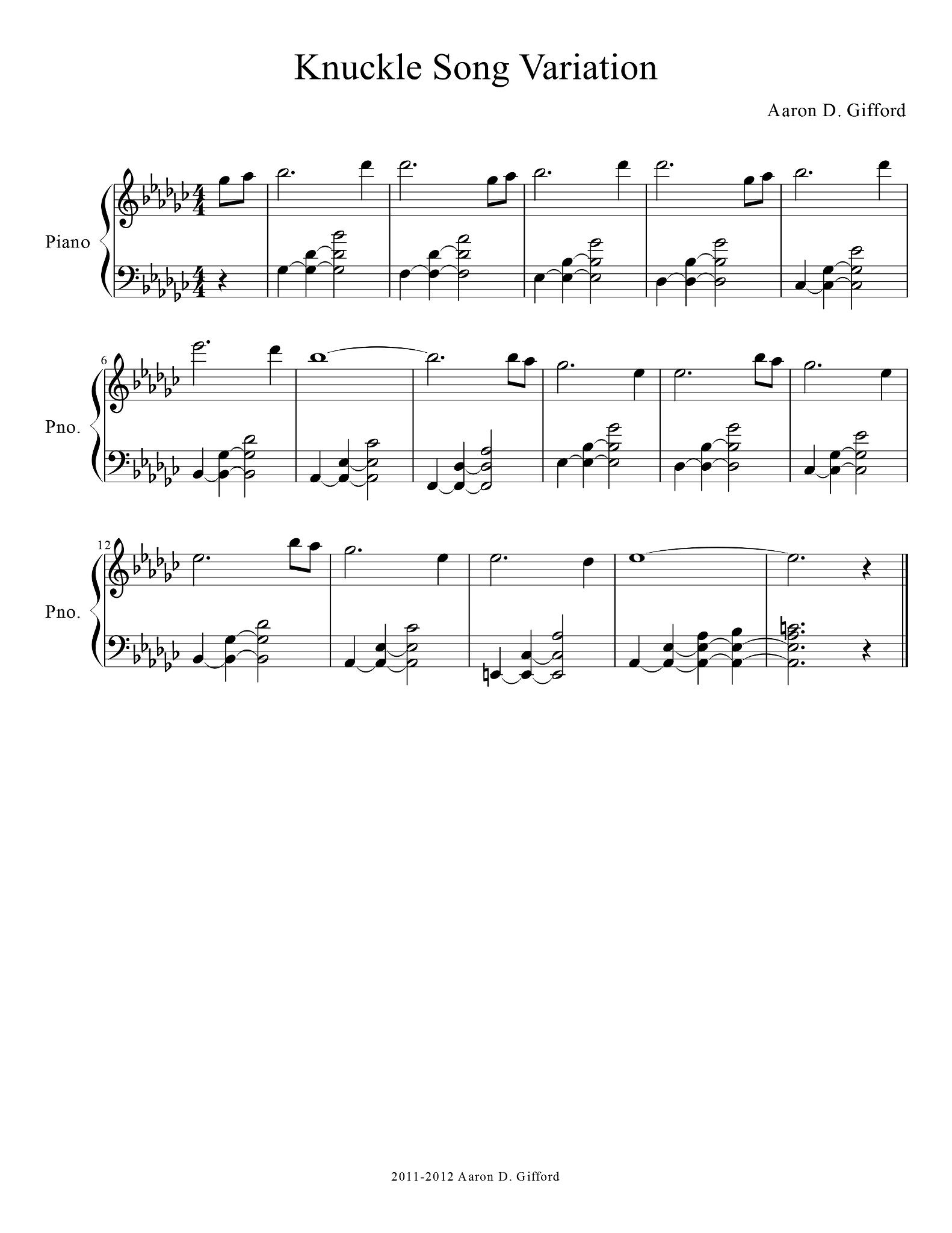 Knuckle Song Variation by Aaron D. GiffordOn the night of the 26th (and morning of the 27th) of July, 2012, I had some fun notating my Knuckle Song Variation, and then on Saturday night (and Sunday morning) made a quickie recording of it to share on Facebook. Here's the web page I put up with the music and recording. Knuckle Song Variation by Aaron D. GiffordOn the night of the 26th (and morning of the 27th) of July, 2012, I had some fun notating my Knuckle Song Variation, and then on Saturday night (and Sunday morning) made a quickie recording of it to share on Facebook. Here's the web page I put up with the music and recording.
This was a lot of fun to do! Click here to hear the song. Incandescent to Compact Fluorescent to LED
Saturday, 09 June 2012 9:05 AM MDT
Yakkity Yak
 New hallway light fixture with LED bulbsI hate compact fluorescent light bulbs. Geek that I am, I was an early adopter, buying some of the very first CF bulbs available in St. George over a decade ago. But I quickly discovered that although they claimed they'd last longer than good old-fashioned incandescent bulbs, the only light bulbs in my house (with just one exception) that I had to replace over the course of the next ten years were the expensive CF bulbs. Incandescents for the win! (Oh, and if an incandescent breaks, I don't have to worry about mercury contamination.) New hallway light fixture with LED bulbsI hate compact fluorescent light bulbs. Geek that I am, I was an early adopter, buying some of the very first CF bulbs available in St. George over a decade ago. But I quickly discovered that although they claimed they'd last longer than good old-fashioned incandescent bulbs, the only light bulbs in my house (with just one exception) that I had to replace over the course of the next ten years were the expensive CF bulbs. Incandescents for the win! (Oh, and if an incandescent breaks, I don't have to worry about mercury contamination.)
I can't totally blame the CF bulbs, however (though my emotional repugnance for them remains unabated). The light fixtures where I installed them were fully enclosed, which CF and LED bulbs DO NOT LIKE because they often overheat in such spaces, while incandescents happily endure high temperatures. I've also always been a fan of warm tone light, preferring bulbs that emit white light in the 2700K to 3000K spectrum range like incandescents and halogen. That's probably another reason that in general I've hated CF bulbs. The color of the light produced was always either cold, or when the bulbs attempted to appear warmer, instead of a yellow-gold tinted white light, an odd pinkish hue was instead emitted. It was a limitation of the phosphors in the CF bulb coatings that convert the invisible ultraviolet light produced by the fluorescing, electrically excited gasses inside. Oh, and depending on the alternating current frequency the CF bulb's electronic circuitry provides, CF bulbs might also have a noticeable flicker. With the entrance of LED bulbs into the market, they too often exhibit similar light spectrum deficiencies and likewise can have flicker issues. But more recently, newer phosphor and LED technologies have finally come to the marketplace, so I decided to give LEDs a try. In order to avoid the enclosed-fixture overheating issues, I decided to replace the light fixtures in my hallway (where the old CF bulbs had all finally died) with an open-air style (a traditional fixture wherein the bulbs mount horizontally and a glass cover attaches below, hiding the bulbs but not completely enclosing them, leaving a gap near the ceiling surface all the way around). So off to Lowes I went. I only made one mistake—I didn't carefully read the packaging and so the two fixtures I bought for just under $30.00 each were for a different, smaller light bulb (the sockets weren't the ordinary A19 style). As my sister observed, I did the "man" thing, and instead of repackaging the fixture and returning it, I fixed it. I MacGyver my old fixture base mount and sockets with the new fixture's threaded, hollow central bolt structure (on which the glass cover hangs). So now I've got two new, working light fixtures installed using parts from my old and parts from the new. Yeah! I also grabbed four $10 40-watt-equivalent 3000K LED light bulbs and installed 'em. I must say that I'm pleased. The lighting looks pretty good. While the bulbs do suffer ever-so-slightly from the pinkish-tint problem, with the new light fixture covers in place, and with the old (ugly, but not really visible) gold light fixture base behind them, everything combines to overcome this issue, bathing my hallway in a pleasing, warm white light. Not bad, LEDs, and the price wasn't too terrible either. $40 for bulbs, $60 for fixtures, and my hallway is now fully illuminated with the equivalent of 160 watts, but only consuming about 30 watts. That really appeals to the technology geek in me! I like my new lights! Viral Stories Fail to Give Credit (Cab Ride Story)
Wednesday, 09 May 2012 8:23 AM MDT
Yakkity Yak
 Photo Copyright © by Guian Bolisay (Instant Vantage) Photo Copyright © by Guian Bolisay (Instant Vantage)
Photo and this 'blog article/post are both licensed under the Attribution-ShareAlike 2.0 Generic (CC BY-SA 2.0) license.Recently on Facebook, someone posted a story about a New York City cab driver who gave a terminal elderly woman a ride that was touching and heart warming. It was a great story! When I first read it, I immediately wondered, "Is this a true story, or fiction?" Unfortunately, the author's name was missing from the story. Sadly, it seems some people, when they share something they like, they remove or omit the original source of the very thing they share, giving no credit to the author, photographer, artist, composer, or creator. They don't include any reference to an original source either. This is one of my pet peeves: NOT giving credit where credit is due. That made it quite difficult for me to figure out if the story was fiction or true, or some variant between the two (i.e. a dramatization of something based on a true event). After some significant searching around the 'net, I eventually learned that the story's author was Kent Nerburn, and that it was originally published in 1999 in Kent's book, Make Me an Instrument of Your Peace: Living in the Spirit of the Prayer of St. Francis. I ran across Kent's web site where he has 'blogged about the story, confirming that the story is in fact a TRUE STORY relating an actual incident from his own life. The story has been circulating via email and web sites, often without crediting the author, since the 1990s. Recently it's gone viral. That may have prompted the recent republication of the story in the Huffington Post. Kent's story "The Cab Ride I'll Never Forget" can now be read online at the Huffington Post here:And in case you still are skeptical, the urban myth-busting web site, Snopes, has likewise confirmed the story is TRUE. If you ever run across something you want to share with others, please be sure to include credit. I would also recommend mentioning where you found it, so if the author or creator is not listed in the source where you found it, someone could potentially trace backwards following sources to find the original. Aaron out. Late Spring Hike Up Shinob Kibe
Monday, 30 April 2012 10:53 PM MDT
Yakkity Yak, Astounding Adventures
 Desert Cactus in Bloom Desert Cactus in Bloom
Monday morning I went hiking up the nearby Shinob Kibe mesa in Washington, Utah. Though most desert flowers had long since dried out, there were still some splashes of color in bloom along the path. With camera in hand, I went a little snap-happy, then posted the results on Facebook. Here is my Facebook photo album of my Shinob Kibe hike. Kolob Reservoir in Autumn - Wallpaper by Aaron D. Gifford - iPad3-sized, 2048x1536
Tuesday, 17 April 2012 11:40 AM MDT
Yakkity Yak
 Kolob Reservoir in Autumn Kolob Reservoir in Autumn
Direct downnload link: Kolob Reservoir in Autumn - Kolob Reservoir, Utah - October 16, 2010 - Copyright 2010 by Aaron D. Gifford - 2048x1536 - www.aarongifford.com.jpg This photo is mine, taken on Saturday October 16, 2010 while visiting Kolob Reservoir in Utah with my family. That autumn afternoon, I took a stroll around the lake to take in the fabulous foliage bedecked in autumn colors, and managed a few lucky pictures in the process. This was one of them that captures nearly perfectly the beauty of that day. This image may be freely used for personal, non-commercial use as a desktop or device background. If you wish to use it as a background or image on a non-commercial web site, click the "Contact Me" link on the left-hand side and ask me for permission (and include the URL of the web page(s) you wish to use the image on). For most non-commercial uses I'll most likely allow it if you embed the image using my server URL as the image source. Exceptions would be those web sites that I find distasteful or offensive. Any other uses will also require written permission from me. Thanks! Fidelity.com Security Breach - Private Information Compromised
Monday, 26 March 2012 1:42 PM MDT
Yakkity Yak
Back in December 2011, I shared how Equifax had leaked private, personal information to persons unknown on the Internet.
Sadly, another large corporation entrusted with monetary and other assets by many people, seems to have done the same thing. That company? Fidelity via their online web site fidelity.com. How do I know? As with Equifax, I had an online access account set up with them and it used a unique, never-shared-with-anyone-else, secure email address dedicated exclusively for use communicating with Fidelity.com. Incident #1: On or Before 23 August 2011 Suddenly,out of the blue, last summer in August 2011, that address started receiving junk email from party or parties unrelated to Fidelity and my account there. The only way that could have happened was if Fidelity had leaked my private, personal information, or a third party entrusted by Fidelity with my information had leaked it. I informed Fidelity and immediately changed my email address to a new, secure, hard-to-guess, exclusively-for-use-to-communicate-with-Fidelity address. I didn't hear back from Fidelity, but I hoped they took my alert to heart and corrected the security breach at Fidelity. Incident #2: On or before 26 March 2012 Imagine my surprise and disillusionment when today I discovered junk mail addressed to my supposedly-secure-since-August new email address, one that only Fidelity had access to! Sorry, Fidelity, YOU BLEW IT! That's twice you have apparently leaked my personal private information without authorization! That is highly indicative of a security breach somewhere, either directly at Fidelity.com, or with affiliated parties that provide key services to Fidelity users. MY REQUEST TO FIDELITY: Fidelity, please take this seriously. Please immediately investigate and track down where the leak is. Plug that leak! This is VITAL. It could be a symptom of a deeper leak of information. Don't suppose that just because the information leaked was an e-mail address that it's okay to ignore this! Once someone knows an email address associated with a Fidelity account, that's one step closer a potential malicious thief is to stealing that account or stealing assets from it! HOW CAN I TRUST YOU? Fidelity, do I dare keep assets with you? Do I dare use your financial services if you can't keep my information safe, private, and secure? UPDATE: (Message from Fidelity received 13 April 2012) To: Aaron Gifford
I'm glad they're taking this seriously.
Subject: RE: Fidelity and Spam email follow up Date: 04/13/2012 03:05 PM EDT Dear Mr. Gifford: I am writing just to touch base with you, regarding the blatant Spam addressed to the email account that you have shared only with Fidelity. Thank you for the quality of your report and the inclusion of technical detail. We want you to understand we take your concern seriously, and are investigating your report aggressively as we are equally eager to uncover the root cause. Have a great weekend, Mr. Gifford, and thank you for being a valuable customer with us! Sincerely, Dawna [Last name omitted by Aaron] Fidelity Brokerage Services LLC, Member NYSE, SIPC What Happened, VLC? With Version 2.0 You Botched It!
Saturday, 25 February 2012 10:59 AM MST
Yakkity Yak
First, VLC Player is a sweet piece of free software, able to play just about any sort of media file thrown at it, unlike certain products I shouldn't mention from Microsoft (*cough* Windows Media Player *cough* *cough*). It's the go-to player for music and video for me.
And with the recent release of version 2.0, some advancements are very welcome. HOWEVER for some reason the File Input access module no longer has a caching or buffer size setting. That is a huge problem, VLC developers! For those like me who have a media server that shares music on the LAN using SMB file sharing, mounting shared folders as drives under Windows. Sometimes the back-end server gets overloaded with I/O requests and that can cause music or video to stutter, pause, and look/sound bad. In the past, all I had to do was bump up the caching/buffer size to a very large size, because the server generally can feed the video source just fine so long as the playback client (VLC in this case) buffers enough. But with version 2.0 I can no longer find a buffer/cache setting for the File Input access module. It shows up nowhere. What gives, VLC? So now VLC is an awful player if for any reason there's a lot of I/O on my back end server (like, for instance, right now, while my server's ZFS pool is doing a scrub, a very I/O intensive process). Even playing a simple compressed MP3 is stuttering. That's just stupid and poor software engineering VLC folks! Your otherwise-perfect product now has a giant flaw! Were I authoring a File input module, I'd take a look at how much free system memory was available, pick an input buffer size from a default setting, then watch playback. By keeping track of the buffer's post-start-up high water mark (i.e. the maximum the buffer was ever filled to, up to 100% after playback started, excluding any pre-playback buffer pre-fill), then should we ever bottom-out (the buffer hit zero and playback sutters), I'd automagically grow the buffer size, perhaps double it, if the high-water mark was 95% or higher. I'd reset the high water mark, and watch anew. That would limit stuttering if the underlying file reads were sporadic (jittery) but the base filesystem was still able to mostly fill the buffer at some point. So, VLC, why not? PLEASE fix this! Otherwise I'm going to have to downgrade to 1.x. This one's a deal-killer! P.S. It turns out a feature request, ticket #2983, was made a long time ago regarding this issue and automating the buffer sizing under the 1.x versions. It is marked as "fixed" with this lame developer cop-out: "This is not fixable on Windows for lack of a statvfs equivalent." Lame! That's not true. One doesn't need statvfs() to keep track of historic buffer input/output rates. It does in fact require more work to implement, and I totally get that this is a volunteer open-source project. But instead of closing the ticket as "fixed" when it is not, it should merely have been left open until such time as someone got an itch to implement it. Annoying ticket closer!
Page 1 of 18
| |